|
|
 |
SUDO_KILLER |
| A tool to identify and exploit sudo rules misconfigurations and vulnerabilities. |
|
|
|
|
|
|
|
|
 |
PhoneInfoga |
| Information gathering framework for phone numbers. |
|
|
 |
Responder |
| Responder is a LLMNR, NBT-NS and MDNS poisoner. |
|
|
 |
ikeforce |
| Command line IPSEC VPN brute forcing tool for Linux. |
|
|
|
|
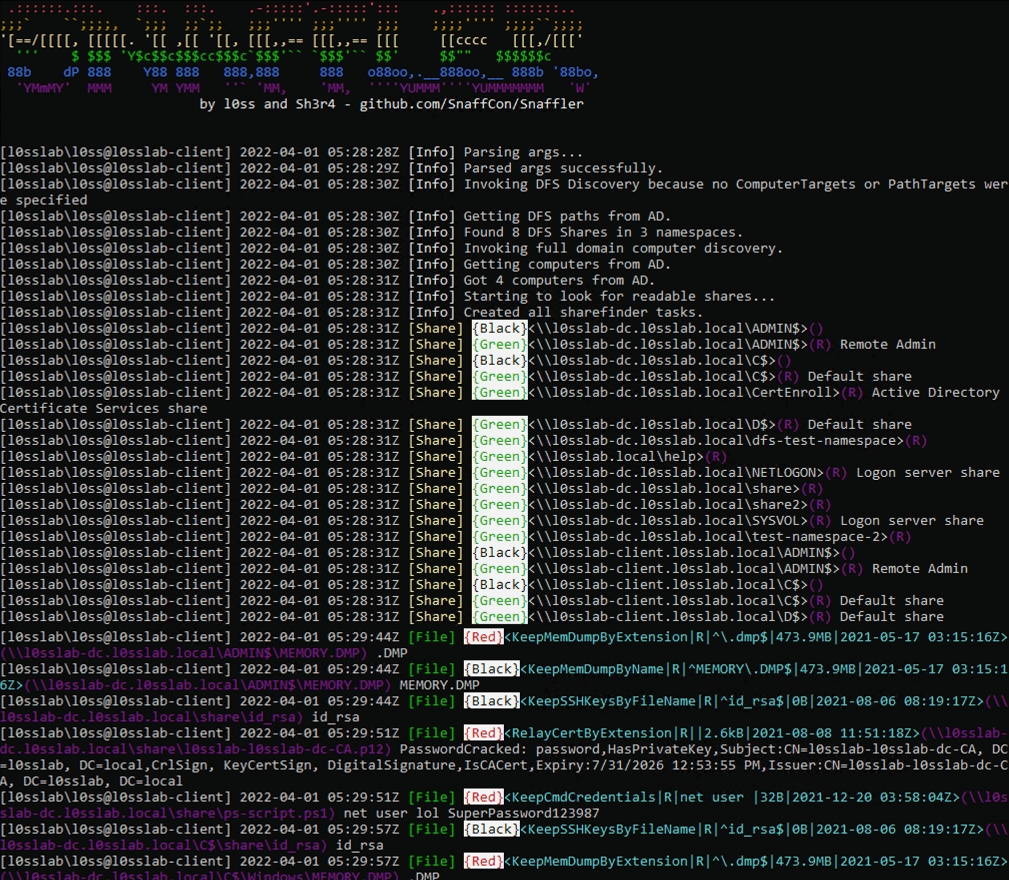 |
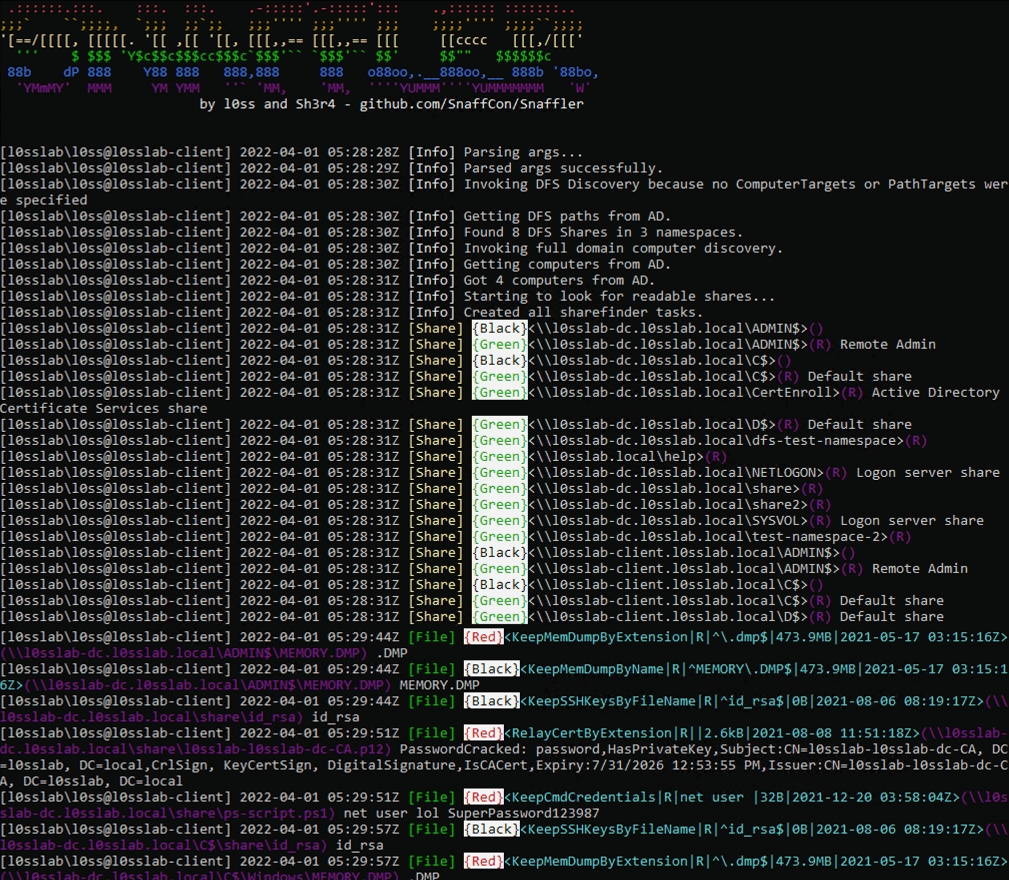
Snaffler |
| A tool to help at finding delicious candy needles in a bunch of horrible boring haystacks. |
|
|
|
|
 |
RidRelay |
| Enumerate usernames on a domain where you have no creds by using SMB relay. |
|
|
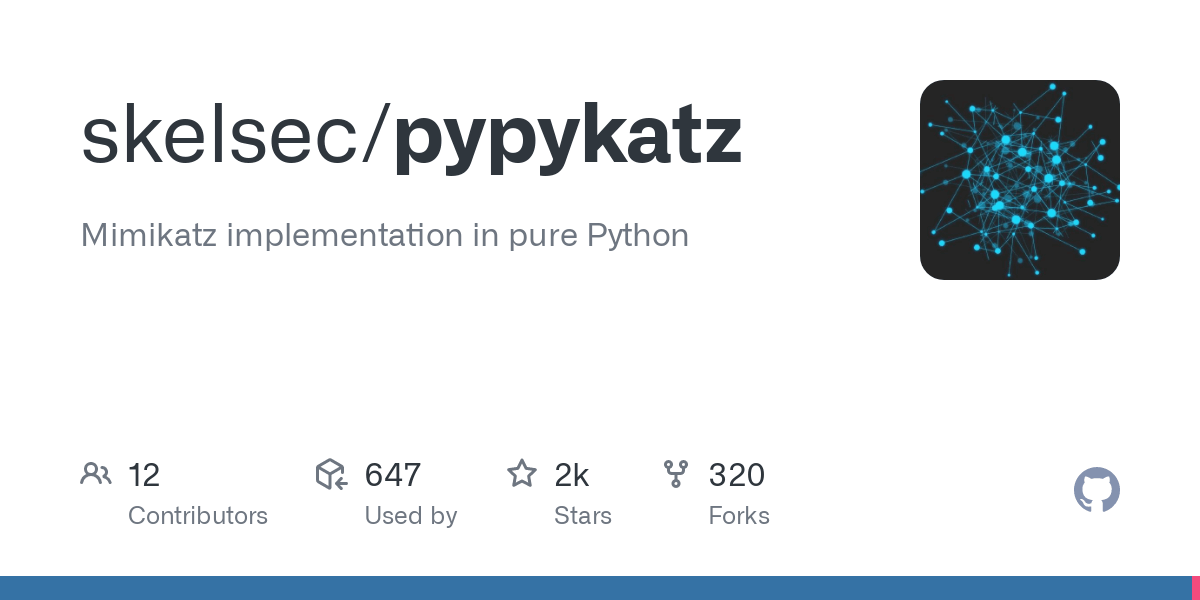 |
pypykatz |
| Mimikatz implementation in pure Python. |
|
|
|
|
 |
Wordsmith |
| Assist with creating tailored wordlists, mostly based on geolocation. |
|
|
 |
SimplyEmail |
| Email recon made fast and easy, with a framework to build on. |
|
|
 |
Rock-ON |
| All in one recon tool that just get a single domain name and do all of the work alone. |
|
|
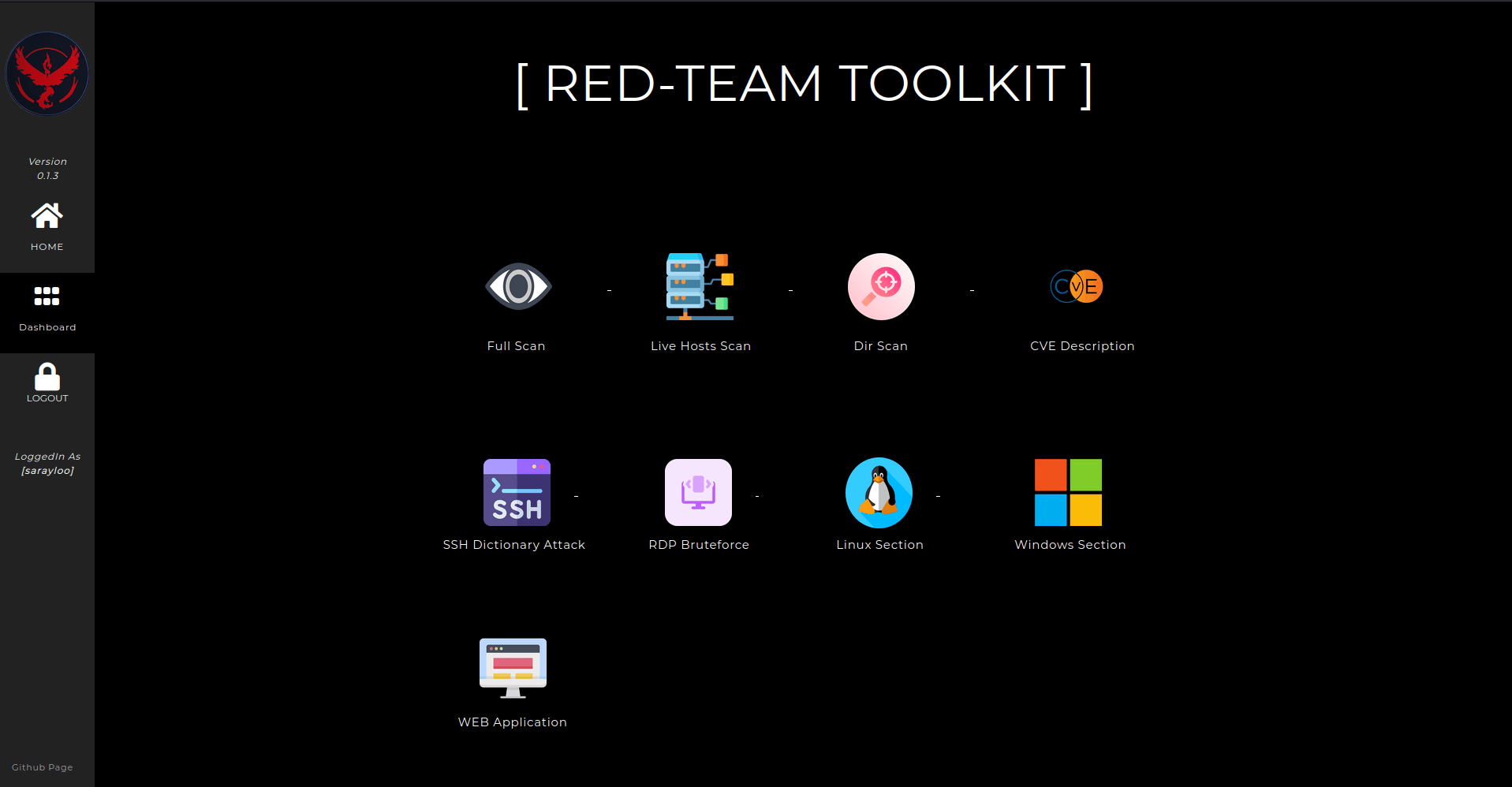 |
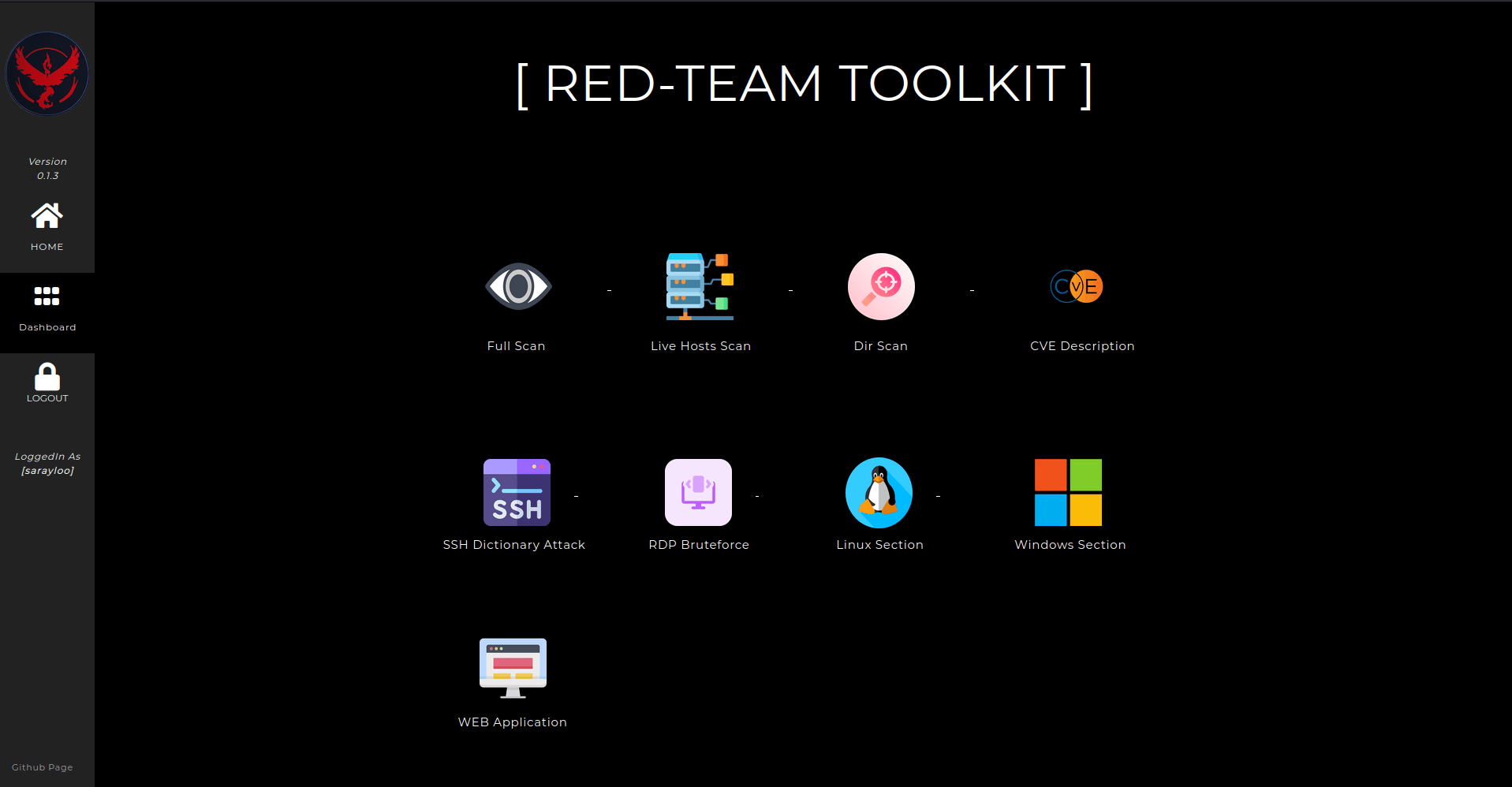
RedTeam_toolkit |
| Open source Django offensive webapp which is keeping the best tools used in the redteaming. |
|
|
|
|
 |
smbmap |
| A handy SMB enumeration tool. |
|
|
 |
celerystalk |
| An asynchronous enumeration & vulnerability scanner. |
|
|
|
|
|
|
 |
reDuh |
| Create a TCP circuit through validly formed HTTP requests. |
|
|
 |
reGeorg |
| Pwn a bastion webserver and create SOCKS proxies through the DMZ. |
|
|
 |
Kwetza |
| Infect an existing Android application with a Meterpreter payload. |
|
|
 |
ADRecon |
| Gather information about the Active Directory and generates a report. |
|
|
 |
AWSloot |
| Pull secrets from an AWS environment. |
|
|
 |
Striker |
| Offensive information and vulnerability scanner. |
|
|
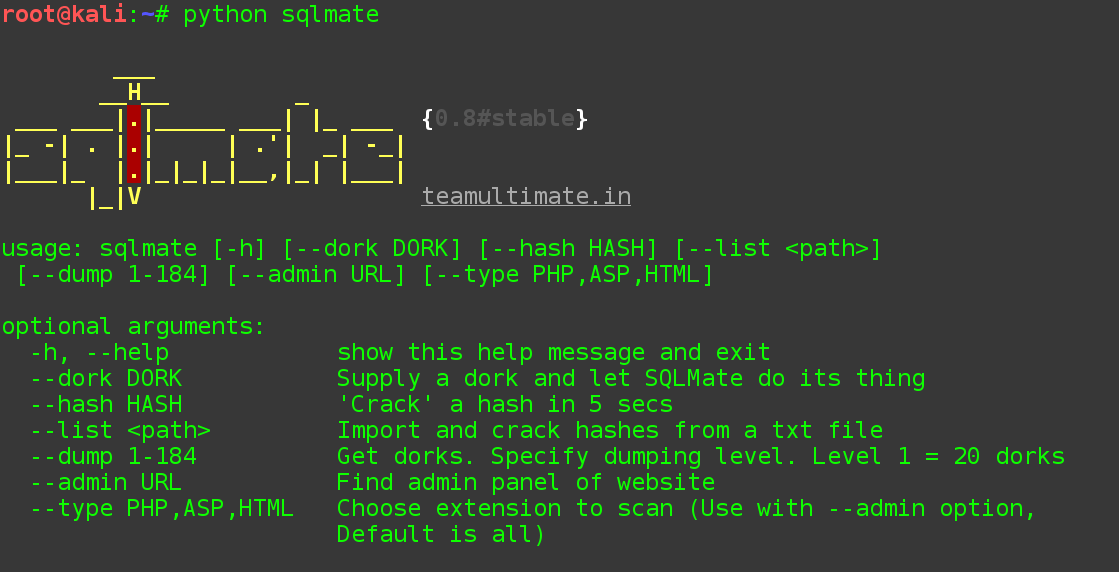 |
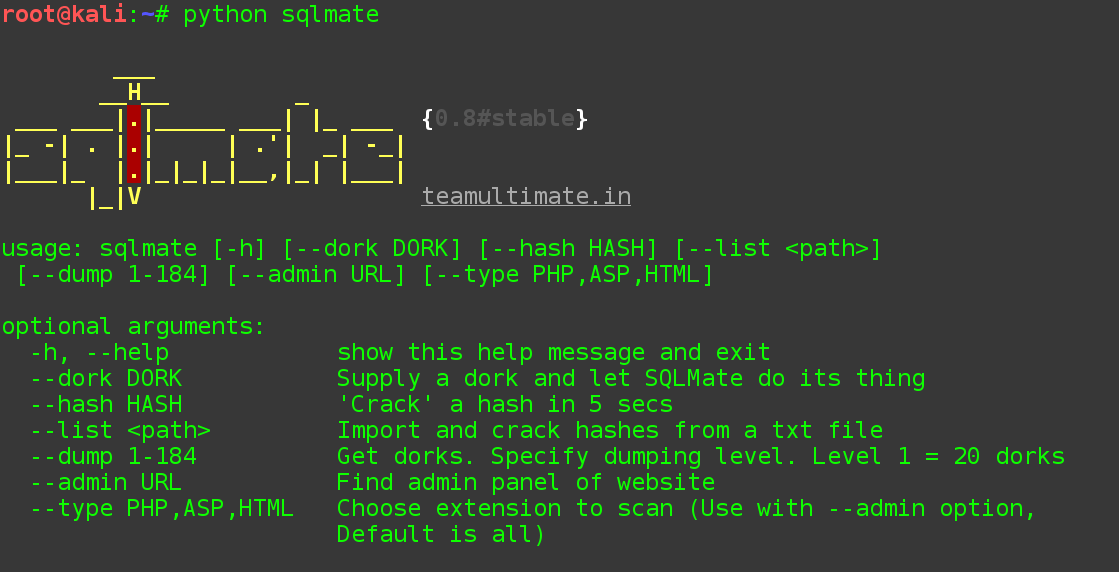
sqlmate |
| A friend of SQLmap which will do what you always expected from SQLmap. |
|
|
 |
favirecon |
| Use favicon.ico to improve your target recon phase. |
|
|
 |
Spy Extension |
| This Chrome extension will read literally everything it can. |
|
|