> Featured this week
featured
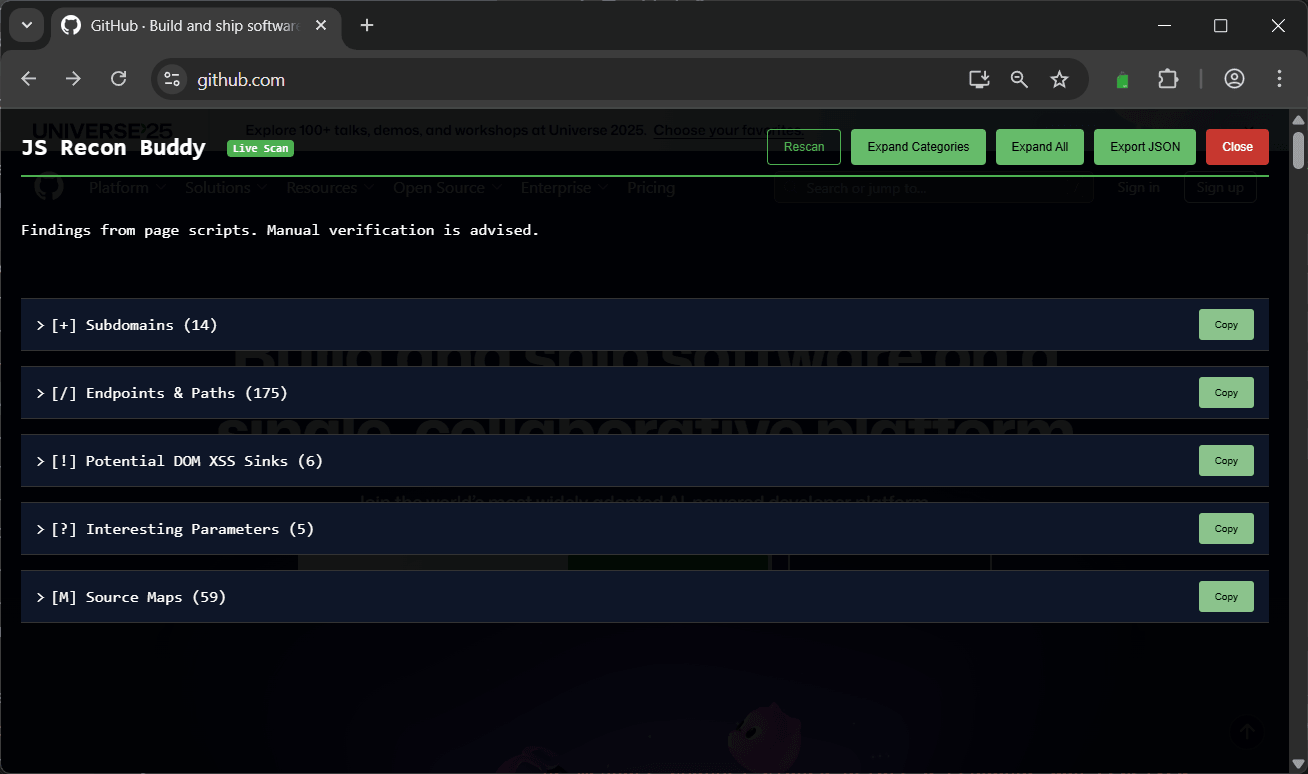
JS Recon Buddy
A passive browser extension to find secrets, endpoints and XSS sinks in JS and HTML.




featured
brutesubs
Automation framework for running multiple open sourced subdomain bruteforcing tools in parallel.
> Last added