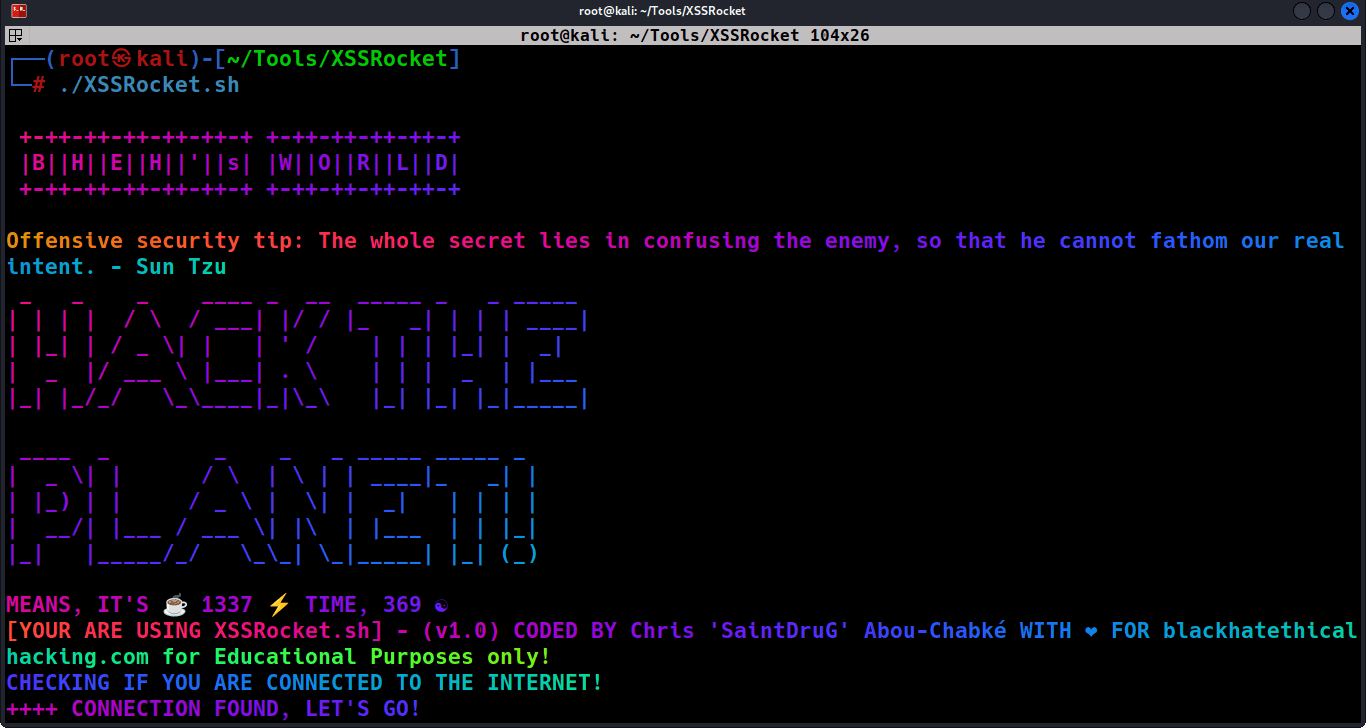
XSSRocket
Written by Black Hat Ethical Hacking and #ChatGPT for offensive security and XSS attacks.
XSS Rocket, uses the Wayback Machine to fetch URLs and filters them based on parameters contained in the URLs. It then filters the URLs with httpx while using multiple Grep and SED patterns to filter only the ones that are alive and valid, removing the contents of the parameters and then uses a remote XSS payload list from Github to send GET requests with the payloads to the filtered URLs injecting them with the XSS Payloads, showcasing the status for 200 and 4XX errors in Red and Green, and creating a Summary for the findings, while saving all the results into a folder that has the same name as the domain name created with all the results, inside it.
Features:
- Supports Stealth Mode using Proxychains, for more reliable attacks against defensive mechanisms
- Automatically fetches URLs from the Wayback Machine
- Filters URLs based on parameters contained in the URLs
- Used httpx to filter only alive URLs and clearing the values for each parameter
- Uses a remote XSS payload list from Github
- Installs all requirements needed depending on the architecture as it gets new updates
- Sends GET requests with payload list to URLs
- Detects and reports possible XSS vulnerabilities
- Creates a folder with the domain name to save results
- Prints final message with number of possible vulnerable URLs and a Summary
- Saves result URLs in a file
- Display a random Sun Tzu quote for offensive security
- Check if the user is connected to the internet before running the tool
- Provides a way to append payloads to the URLs
- Output the full URL with payload
This tool with also display a summary feature that displays the total number of possible XSS injections found, along with a list of affected URLs, the payload used, and the response code, at the end.







