ShadowSpray
Spray shadow credentials across an entire domain.
How this tool works:
- Login to the domain with the supplied credentials (Or use the current session).
- Check that the domain functional level is 2016 (Otherwise stop since the Shadow Credentials attack won't work)
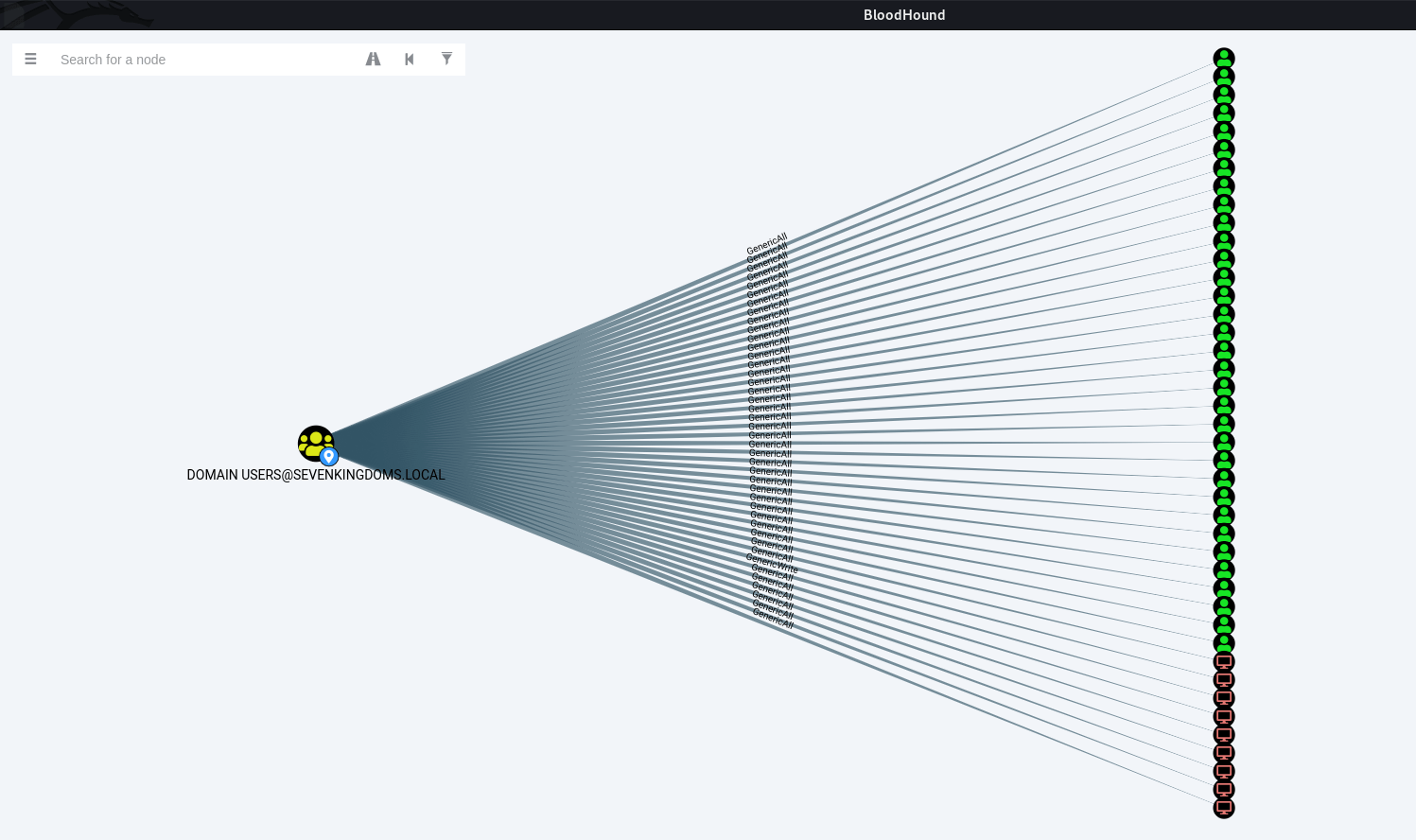
- Gather a list of all the objects in the domain (users and computers) from LDAP.
- For every object in the list do the following:
* Try to add KeyCredential to the object's "msDS-KeyCredentialLink" attribute.
* If the above is successful, use PKINIT to request a TGT using the added KeyCredential.
* If the above is successful, perform an UnPACTheHash attack to reveal the user/computer NT hash.
* If --RestoreShadowCred was specified: Remove the added KeyCredential (clean up after yourself...)
- If --Recursive was specified: Do the same process using each of the user/computer accounts we successfully owned.
ShadowSpray supports CTRL+C so if at any point you wish to stop the execution just hit CTRL+C and ShadowSpray will display the NT Hashes recovered so far before exiting (as shown in the demo below).







