off-by-slash
Burp extension to detect alias traversal via NGINX misconfiguration at scale.
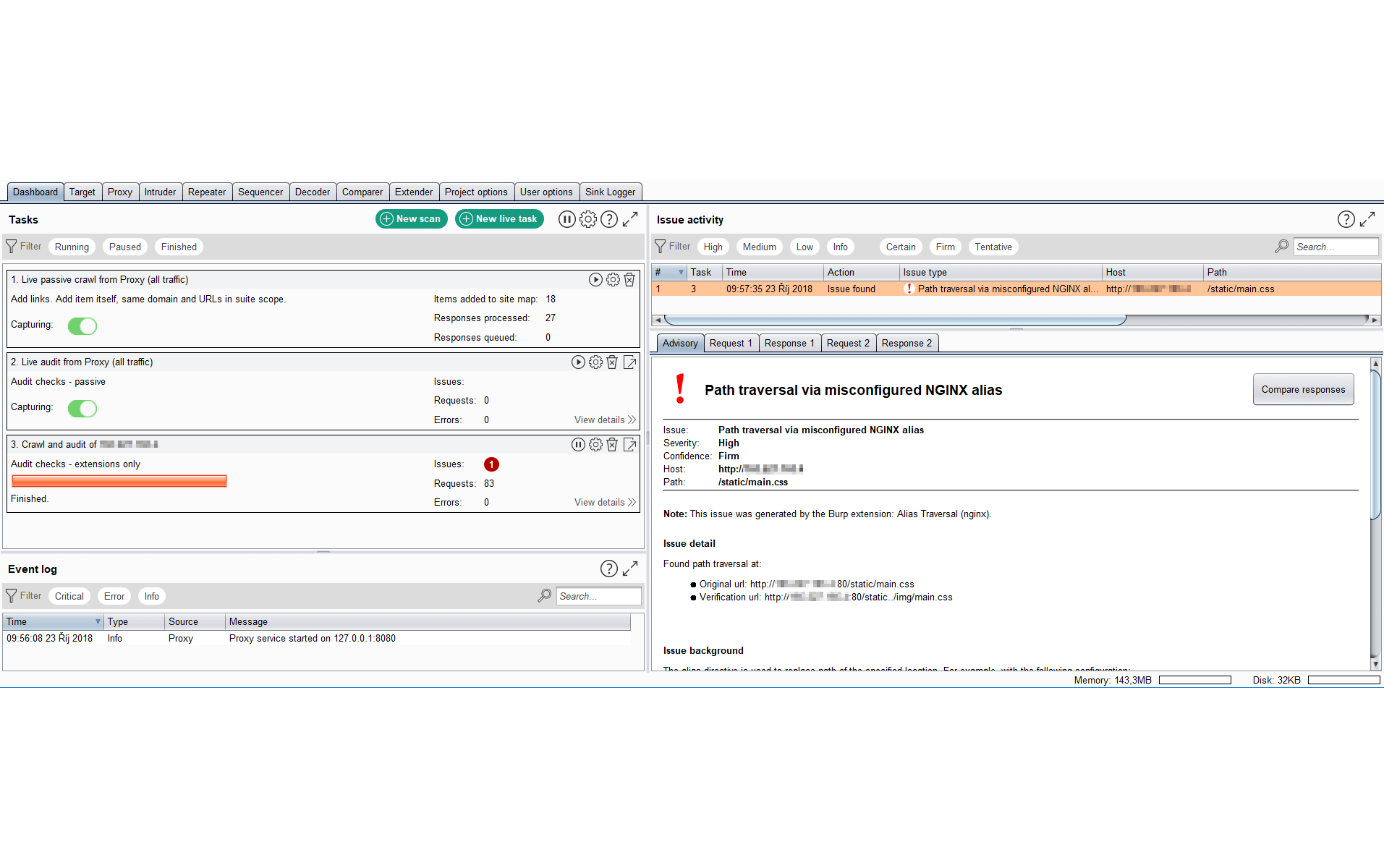
The extension implements an active scanner check. Simply run a new scan, preferably with an "Audit checks - extensions only" configuration, on static resources identified via Burp's crawler.
A server is assumed to be vulnerable if a request to an existing path returns the same response as the original path. To eliminate false positives the misconfiguration has to be confirmed by successfully requesting an existing resource via path traversal.







