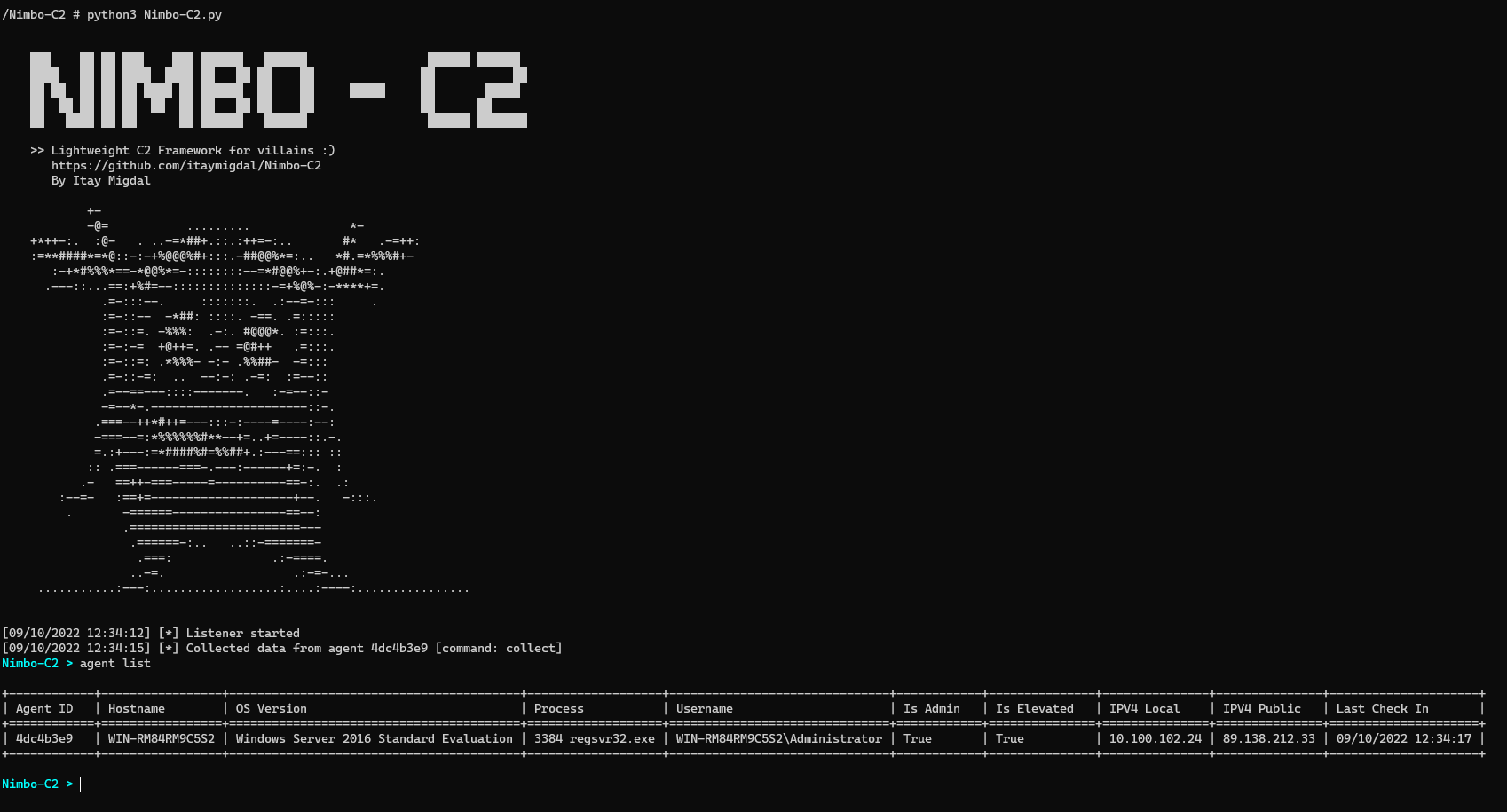
Nimbo-C2
Yet another (simple and lightweight) C2 framework.
Features:
- Build EXE, DLL, ELF payloads.
- Encrypted implant configuration and strings using NimProtect.
- Packing payloads using UPX and obfuscate the PE section names (UPX0, UPX1) to make detection and unpacking harder.
- Encrypted HTTP communication (AES in CBC mode, key hardcoded in the agent and configurable by the config.jsonc).
- Auto-completion in the C2 Console for convenient interaction.
- In-memory Powershell commands execution.
- File download and upload commands.
- Built-in discovery commands.
- Screenshot taking, clipboard stealing, audio recording.
- Memory evasion techniques like NTDLL unhooking, ETW & AMSI patching.
- LSASS and SAM hives dumping.
- Shellcode injection.
- Inline .NET assemblies execution.
- Persistence capabilities.
- UAC bypass methods.
- ELF loading using memfd in 2 modes.
- And more !







