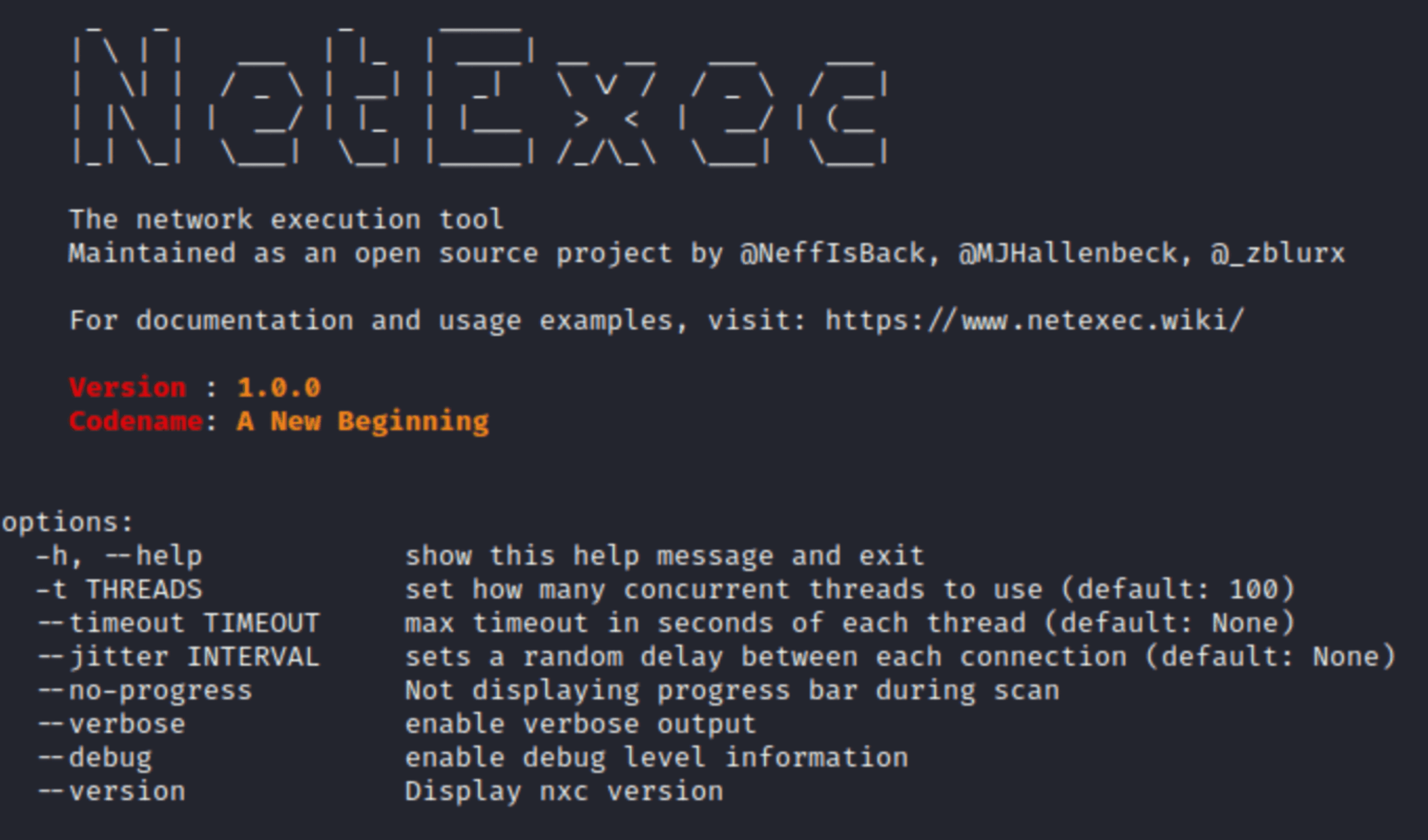
NetExec
Network service exploitation tool that helps automate assessing the security of large networks.
Each protocol has its own database which makes things much more sane and allows for some awesome possibilities. Additionally, there are workspaces (like Metasploit), to separate different engagements/pentests.
Protocols available: smb, ssh, ldap, ftp, wmi, winrm, rdp, vnc, mssql.
The tool ships with a secondary command line script which abstracts interacting with the back-end database.







