

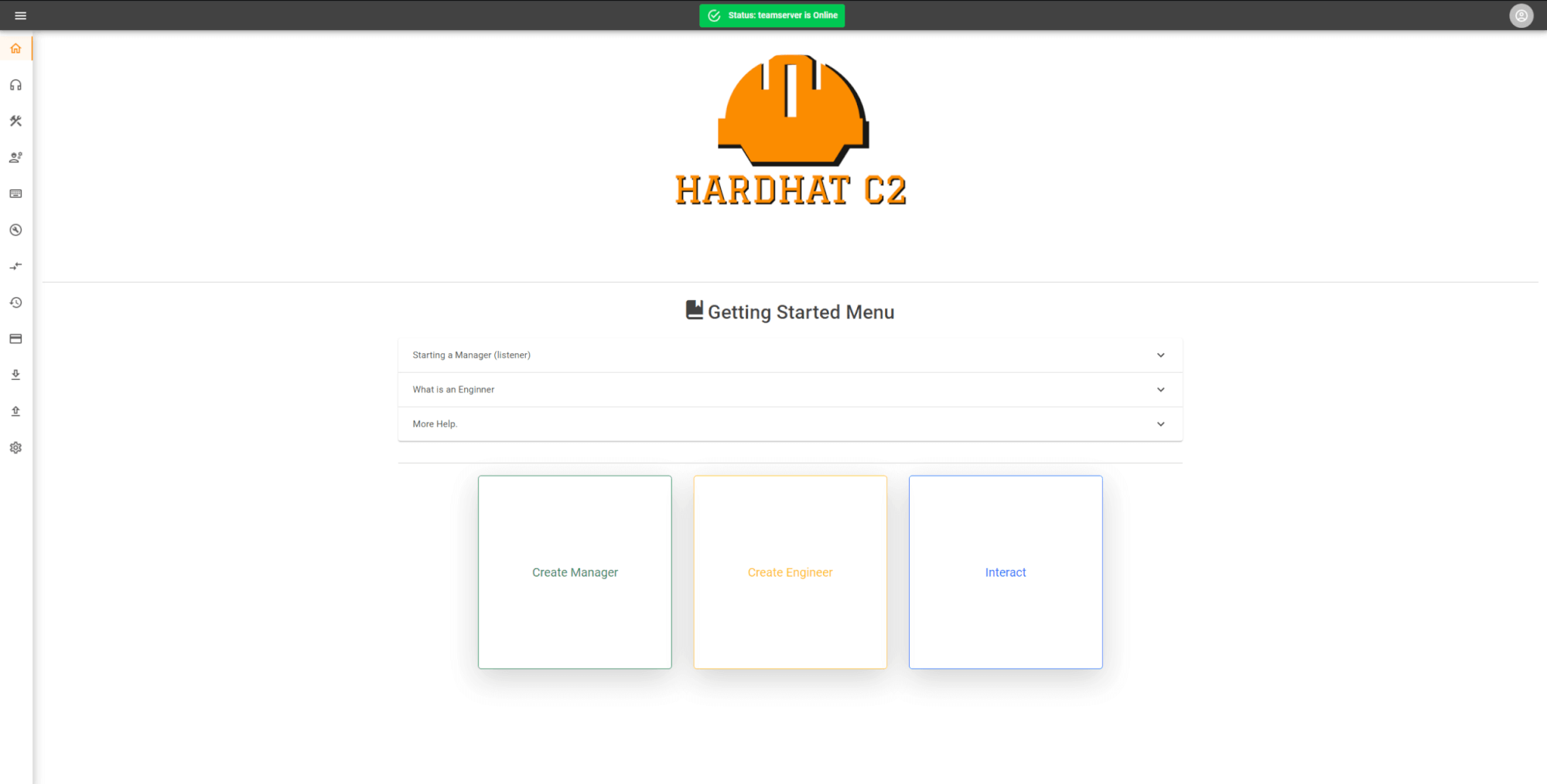
HardHat C2
A cross-platform, collaborative, Command & Control framework.
HardHat is a multiplayer C# .NET-based command and control framework. Designed to aid in red team engagements and penetration testing. HardHat aims to improve the quality of life factors during engagements by providing an easy-to-use but still robust C2 framework.
It contains three primary components, an ASP.NET teamserver, a blazor .NET client, and C# based implants.
Features:
- Per-operator accounts with account tiers to allow customized access control and features, including view-only guest modes, team-lead opsec approval(WIP), and admin - accounts for general operation management.
- Managers (Listeners)
- Dynamic Payload Generation (Exe, Dll, shellcode, PowerShell command)
- Creation & editing of C2 profiles on the fly in the client
- Customization of payload generation
- File upload & Downloads
- Graph View
- File Browser GUI
- Event Log
- JSON logging for events & tasks
- Loot tracking (Creds, downloads)
- IOC tracing
- Pivot proxies (SOCKS 4a, Port forwards)
- Cred store
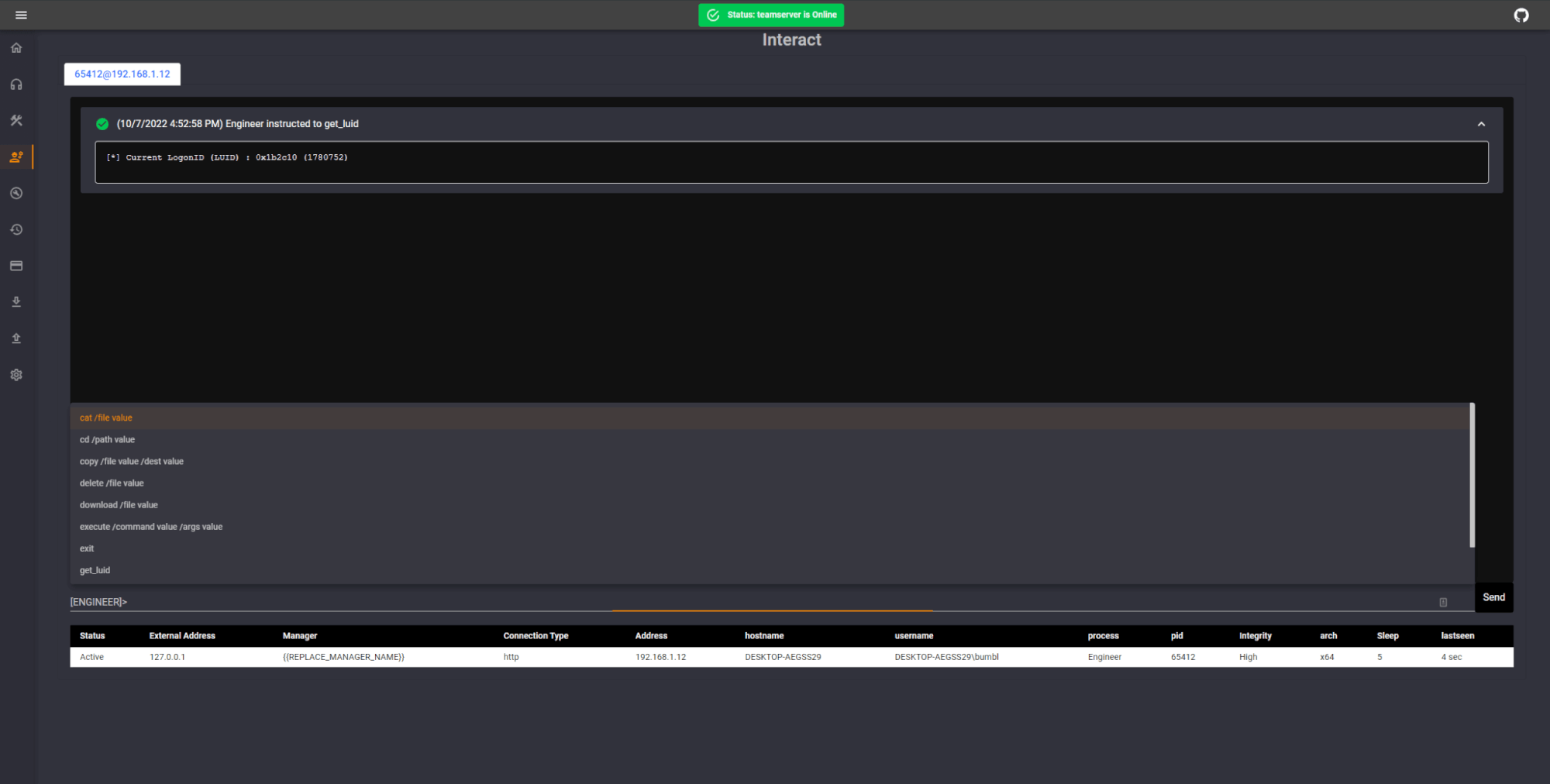
- Autocomplete command history
- Detailed help command
- Interactive bash terminal command if the client is on linux or powershell on windows, this allows automatic parsing and logging of terminal commands like proxychains
- Persistent database storage of teamserver items (User accounts, Managers, Engineers, Events, tasks, creds, downloads, uploads, etc. )
- Recon Entity Tracking (track info about users/devices, random metadata as needed)
- Shared files for some commands (see teamserver page for details)
- tab-based interact window for command issuing
- table-based output option for some commands like ls, ps, etc.
- Auto parsing of output from seatbelt to create "recon entities" and fill entries to reference back to later easily
- Dark and Light 🤮 theme







