

Goby
Network security technology that achieves rapid security emergency.
The richest device rule set:
More than 100,000 rule identification engines are pre-set in Goby, which can identify and classify hardware equipment and software business system automatically and comprehensively analyze the business system that exists in a network. It currently supports more than 100,000 devices and business systems. Hardware coverage: network equipment, internet of things equipment, network security products, office equipment, etc. Software coverage: CRM, CMS, EMAIL, OA system, etc.
Most lightweight protocol identification:
More than 200 protocol identification engines are pre-set in Goby, covering networking protocol, database protocol, IoT protocol, ICS protocol, etc. Through very lightweight Iperf, it can quickly analyze the protocol information corresponding to the port, with fast speed and little impact on target equipment.
Port grouping based on rich attack and defense experience
Vulnerability framework based on daily community updates:
The vulnerability engine with the most effective attack is pre-set in Goby, covering the critical vulnerabilities such as Weblogic and Tomcat. A large amount of vulnerability information is generated from the Internet (such as CVE) , which are screened and updated on daily basis to identify the ones that would be used for real attacks. Goby also provides a customizable vulnerability checking framework. Security practitioners around the world are motivated to contribute POC to ensure continuous emergency response capability. Meanwhile, We believe that the real-effect-based checks are more valuable than version-based comparisons.
The most comprehensive default password detection:
Almost any device will have a default account or even a backdoor account, and the traditional brute force attack mode is not optimal. Pre-set account information of more than 1,000 devices are pre-set in Goby for targeted inspection, ensuring the accuracy and efficiency of risk identification. Goby has built-in brute force attack testing of custom dictionaries for various protocols.
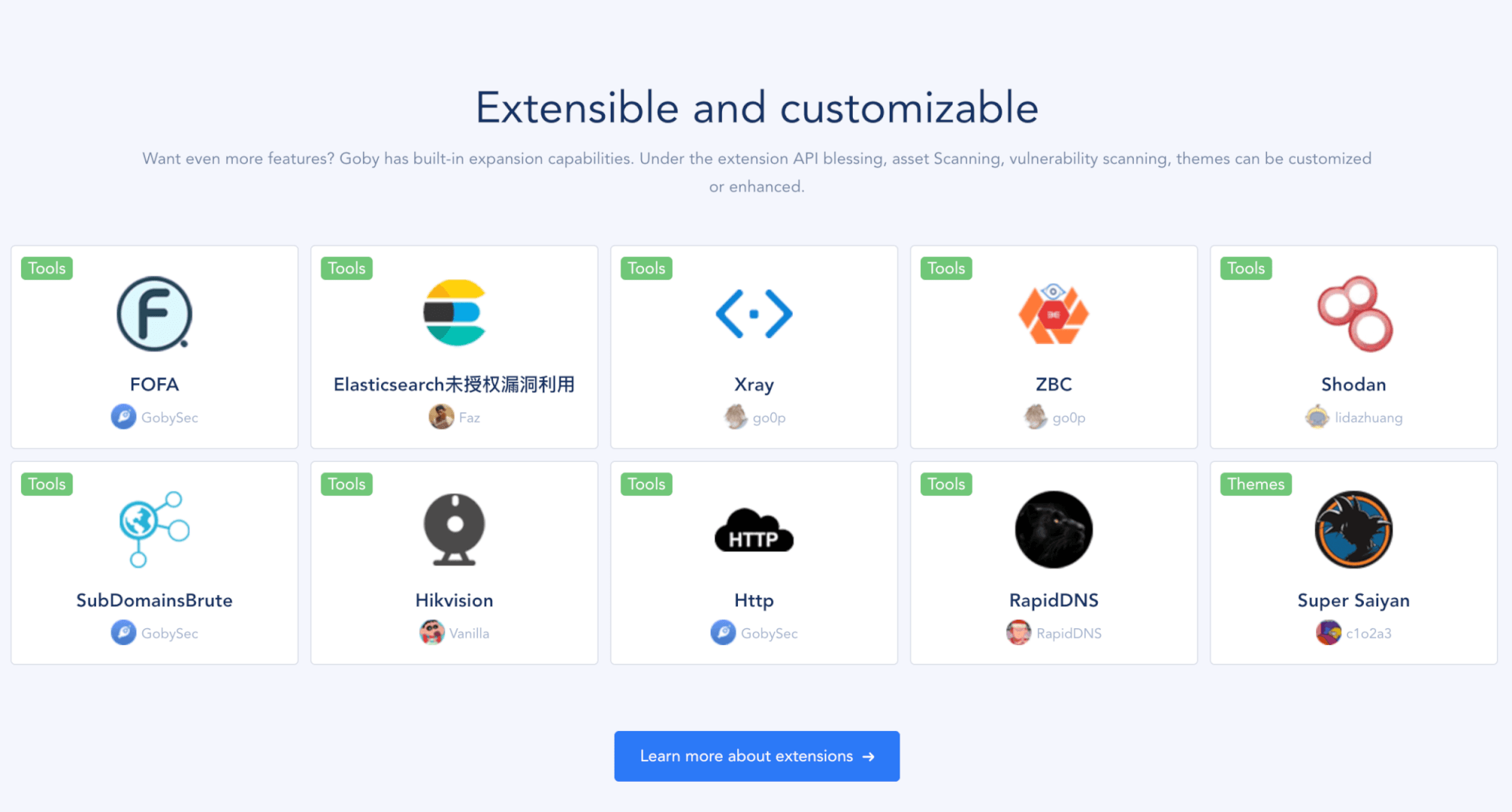
Extensible and customizable:
Goby has built-in expansion capabilities. Under the extension API blessing, asset Scanning, vulnerability scanning, themes can be customized or enhanced.







